The following article provides information on working with Malware or Virus infected systems.
Table of Contents:
- What level of support is possible for Malware and Virus infection Issues?
- What is the difference between Malware and a virus?
- What are the most common symptoms of a Malware of Virus infection?
- Malware Detection/system usability steps
- General Removal Guide
- Scanning Software
- Removing the Infection
- Prevent Re-Infection
- Other Removal Options
What level of support is possible for Malware and Virus infection Issues?
CyberPowerPC’s standard practice has historically been to recommend a clean install of the Operating System (OS), once Malware or a Virus has been detected. This will resolve an infection issue 100% of the time.
Under a ProSupport warranty, our Technical support should always investigate and identify the infection has taken place. They should attempt to get the system to a usable state in order to run antivirus scans or determine if a clean reinstall should take place due to the level of infection on the system.
What is the difference between Malware and a virus?
Malware, or malicious software, has become a catch-all term for several different types of infections. Some will install themselves and create a simulated infection, corruption, or hardware failure, therefore tricking you into purchasing their product to resolve the issue. This type is known as hostage-ware, ransom-ware or scare-ware. There are malware infections that simply redirect your browser to sites the creator has chosen or to a website that they are compensated for, based on the number of hits the site receives. Sometimes these infections can hide your entire root drive and all your subdirectories or capture your personal information and communicate back to the creator of the infection.
A virus, which has become a subset of malware, is an actual program that replicates and attaches itself to services or specific applications. Many malware payloads contain a virus file, such as a Trojan or a Worm, to help root the infection. Viruses were once an exclusive type of infection, but now they have been combined into infection packages of malware. Many malware packages incorporate rootkits to embed themselves into the kernel level of the OS, making them stealthy and more difficult to remove.
Many items are often mistaken for system infection. These can include tracking cookies, search hooks, or browser helper objects (BHOs). Although the presence of these can indicate infection, there must be an accompanying loader (EXE) file or kernel mode driver to present to confirm infection.
What are the most common symptoms of a Malware of Virus infection?
Although today’s malware can contain multiple payloads, here are some of the most common signs of infection:
- Onscreen Warnings about system infection from a source other than your antivirus software
- The browser redirects or a complete hijack of the browser
- You can't open any EXE or Microsoft Installer (MSI) files
- The inability to change wallpaper or any desktop settings
- All entries under Start>Programs are empty and/or the C: drive is blank
- The Antivirus icon disappears from the system tray or cannot be started
- Random pop-ups show onscreen either in or out of the browser
- Unusual icons, erroneous start menu, or Device Manager entries appear
Malware Detection/system usability steps
Here are some steps to perform to confirm infection :
-
Ask the question. "Are there any pop-ups, redirects, or messages that have been experienced on the desktop or from the system tray?"
-
Has a recent virus or malware scan been run? If the antivirus or malware removal tools will not run, then this is a positive sign that the system may be infected.
-
If the internet or system is inoperative due to infection, boot to Safe Mode with Networking. (using LAN only.)
-
These programs or any other malware removal tools will not open if the shell extension for EXE’s is blocked in the registry. Right-click the .EXE file and rename the extension to .COM. Attempt to run the tool. If it still will not open, boot to Safe Mode and attempt to run the tool again.
-
If you have an active antivirus subscription, you can attempt to remove the block on the antivirus. Un-checking any malicious entries in Autoruns and rebooting may allow EXE files to run again and you can update and scan with your antivirus. Sometimes a kernel mode driver is installed in Device Manager to block the antivirus software. It usually shows under Plug and Play Devices and you must set Device Manager to Show Hidden Devices.
If positive malware identification is made, you can make use of the options below at this point. Just remember if it doesn't work, we can take you through a clean OS reinstall to resolve the issue.
General Removal Guide
Disconnect your PC from the Internet and don't use it until you're ready to remove the malware.
Think of it like cutting off all communications or putting a patient into a suspended state.
Boot your PC into Safe Mode. Only the minimum required programs and services are loaded in this option. If any malware is set to startup when Windows starts, booting in safe mode should prevent it.
To boot into Windows Safe Mode, Please follow whichever guide below matches your Operating System (OS). This should bring up the Advanced Boot Options menu. Select Safe Mode with Networking and press the Enter key.
You will find that your PC runs faster in Safe Mode. If it does, it could be a sign that your system has a malware infection or it could mean that you have a lot of legitimate programs that normally start up with Windows.
Delete your temporary files before starting any other steps. Doing this could speed up the virus scanning, but it will clear the downloaded virus files and lessen the amount the scanners will have to check. You can do this through the Disk Cleanup utility or from the internet options menu.
Note: If you are using windows 10 and instead of seeing the safe mode screens, the system gives a prompt asking for the Windows 10 product code - please use the link below to troubleshoot Windows 10 Black Screens.
The following link takes you to an article with general steps to take you through the removal of the most often encountered Malware types:
Scanning Software
Sometimes running a scanner is enough to remove most malware infections. You've most likely got an antivirus program active on your PC, you should use another scanner for this check.
If your current antivirus software didn't stop the infection, you can't expect it to find the problem now and we would recommend trying a new program.
There are two main types of antivirus.
- Real-time antivirus programs
-
They constantly watch for malware.
- On-demand scanners
-
They search for malware infections when you open the program manually and run a scan.
The best course of action is to use an on-demand scanner first and then follow up with a full scan by your real-time antivirus program. There are several free and effective on-demand scanners available. You can find a list of the most common ones in the last section of this article.
Removing the Infection
In this guide, we will the use Bitdefender Free Edition as it is a well known and reputable software and offers a convenient free edition. You can find another program if you want something more robust and active in Section 9 below. If you're following this guide then Download the Bitdefender Free Edition program and install it. You will need to reconnect to the Internet for this. Once the download is complete, disconnect from the Internet again. If you can't access the Internet or you can't download Malwarebytes on your PC, then download it on another system and save it to a USB flash drive or CD/DVD and transfer it to the infected PC.
To install Bitdefender correctly on your computer, follow these steps:
1. Double-click the installer file to launch the setup wizard.
2. Please read the End User License Agreement and select I accept the terms of the license agreement. Click Next to continue.
The setup wizard checks your system's security settings and displays the current status. If another antivirus product is detected, you must uninstall it before you can continue.
By default, a quick scan is performed before the Bitdefender components are installed to ensure no active malware is residing on your system. It is highly recommended to allow the scan to be performed. Active malware could disrupt the installation and even cause it to fail.
3. Click Start to begin the installation.
4. Details about the progress of the installation are displayed.
It takes just a few minutes to complete the setup. Once completed, click Finish to close the installer.
Scanning for infection
- Open the Bitdefender application
- On the main screen, click on the Scan Now button in the Antivirus section on the left side of the window.

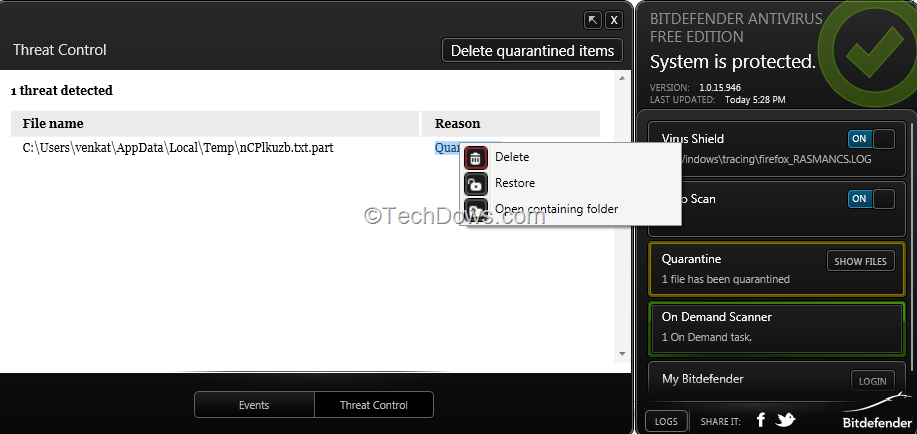
- Once the scan is complete Bitdefender will identify potential threats it has found and quarantined. These are applications or files that it has identified or suspects to be a threat. You can remove these individually by clicking on each file or you can delete them all at once by clicking on Delete quarantined items button at the top.
If your problems persist even after you've run the scan and it has found and removed unwanted files, then follow the advice above and run additional scans with Bitdefender or try some of the other scanners mentioned in Section 9 below. If the malware appears to be gone, run a full scan with your real-time antivirus program to confirm that result.
If you can't seem to remove the malware or if Windows isn't working properly, you may have to reinstall Windows. Please see the appropriate link below for a guide to suit your particular situation.
- How to identify and troubleshoot potential OS reinstall and driver issues on my CyberPowerPC Desktop
Prevent Re-Infection
To minimize the risk of a repeat infection, please pay attention to the steps below :
-
Keep your operating system and applications updated with the latest security patches. On Windows Update, these would be the updates marked as critical and security.
-
When you are reading your email, do not open messages or attachments sent from unknown senders. If you are unsure, it is better to delete it than to expose your system to reinfection.
-
Make sure that you have a real-time antivirus program running on your PC and see that it stays updated. If you don't want to spend money on a paid service, then you can install one of the free programs that are available.
-
Scan any removable media before they are used. (This includes, floppies, CDs, DVDs, Flash USBs, and External HDDs.)
-
Do not download unknown software from the web. The chances of infection from an unknown source is too high a risk.
-
Scan all incoming email attachments or any other file that decide to download - prior to actually using it.
-
Do not open files received via email or chat with the following extensions. .exe, .pif, .com, and .src,
-
In addition to installing traditional antivirus software, you might consider reading the guide below for some basic rules for safe surfing online.
Always double check any online accounts such as online banking, webmail, email, and social networking sites. Look for suspicious activity and change your passwords, you can't tell what info the malware might have passed on.
If you have an automatic backup for your files you will want to run virus scans on the backups to confirm that it didn't back up the infection as well. If virus scans aren't possible such as online backups, you will probably want to delete your old backups and save new versions.
Keep your software current. Make sure that you update them frequently. If you receive any messages about this and aren't sure of their validity, then always contact the company in questions support to clarify it.
Other Removal Options
Once an infection is identified, you have to decide on your next step.
There are several options for resolution :
-
We can offer a CyberPowerPC service technician to do the work for you, but this is a pay for service.
-
We can always reinstall the operating system as well.
-
If the infection is obvious and can be located easily, then you may be able to attempt removal.
If you are able to get online or use another system with the internet, then you check out the following article and tools for further information :
Link to Microsoft's online Tool
Publishers list of Scanner, Cleaner, and other Security Utilities
Article Version DK.01

Comments
0 comments
Article is closed for comments.